Data is not an easy asset to manage. Inside companies, the use of multiple, different IT systems and platforms has led to the emergence of data silos impeding smooth and flawless business processes. When it comes to exchanging and sharing data across company borders, management oftentimes is reluctant due to fear of vendor lock-in – an effect that can be seen particularly when a company is dependent on a certain cloud service provider using proprietary technology.
Wouldn’t it be better to simply lock away one’s data?
The solution appears to be quite simple: If the data receiver uses the same technology or platform as the data owner, the data owner can specify rules on how the data may be used by the data receiver – and even enforce compliance with these rules on a technical level. This way, the data owner can be sure that data sovereignty is guaranteed. But what if the two companies do not find an agreement as to what common technology or platform they should use? In the best case, the two companies have long-standing business relationships with each other, so that the data owner has trust in the data receiver using the data as agreed upon by both parties. Otherwise, it may just seem better for the data owner to simply lock away its data and prevent it from being accessed by others.
A much better solution: the European Industrial Data Space (EIDS)
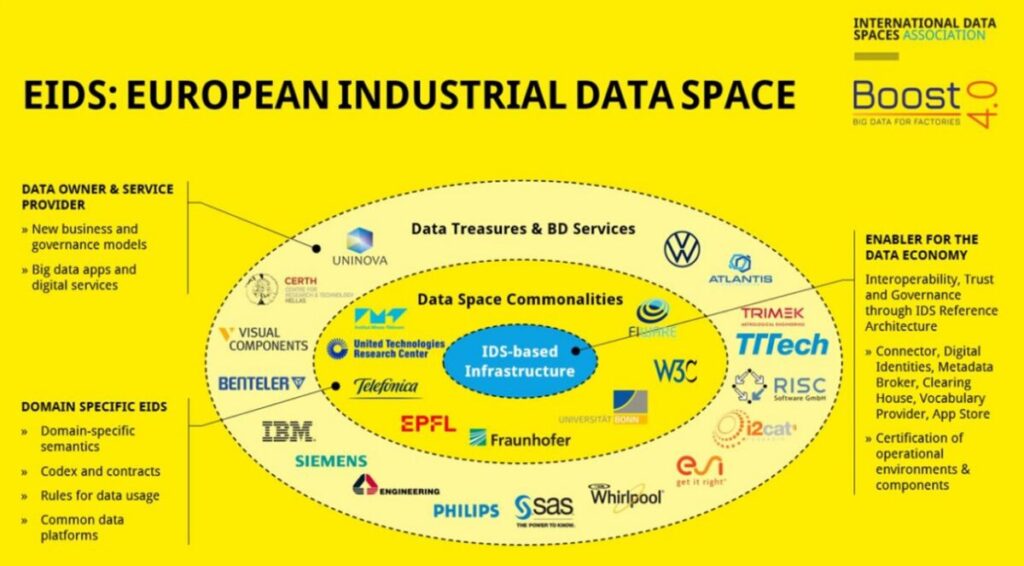
“BOOST 4.0 – Big Data For Factories” is a project in which experts joined forces to develop a solution that helps overcome the dilemma described above. The European Industrial Data Space (EIDS) is based on the IDS Reference Architecture[1], which was developed by the International Data Spaces (IDS) Association and its over 120 member organizations. The Association – operating independently from BOOST 4.0 – aims at giving companies back control over their data. To achieve this goal, it has specified and developed a standard: IDS.
Accessing EIDS via the IDS Connector
Unlike with other platforms, users of EIDS do not need to create an account to be granted access. Instead, each user must install the IDS Connector, which is specified by DIN SPEC 27070[2]. To establish trust among all users of EIDS, not just the technical components (IDS Connectors, applications etc.) are certified against the IDS standard, but also each participating organization or individual itself (especially with regard to the execution environment used).
IDS certification ensures that the software used has no built-in “backdoors“. Furthermore, it creates transparency by assigning a “trust level” to each participant, making the security mechanisms in place there visible for all other participants. This way, each party can decide on a case-by-case basis, i.e. prior to a potential data exchange transaction, if the level of security and trust assigned to a certain organization or individual is sufficient, or if another EIDS participant should be chosen to exchange or share data with.
Finding the right data
The IDS Reference Architecture requires no central data storage entity; instead, the data physically remains with the respective data owner. Such a decentral approach presupposes that each data source is comprehensively described and specified, revealing the value and fitness of the respective data for other EIDS participants. As a data trading platform makes sense only if the participants can actually find the data they are looking for, EIDS uses a function named Metadata Broker, allowing participants to search for the data they need by requesting metadata (i.e. descriptions) of the data. In addition, EIDS offers an App Store, which participants can address if in need of certain applications or data processing services. And, last but not least, participants can use the service of a Vocabulary Provider for retrieving domain-specific ontologies (similar to the semantic web), which is important as smart factories and the machines therein need to interpret large volumes of data.
EIDS – a milestone on the way to the smart factory
Alongside with components supporting participants in their search for the right data, EIDS encompasses a number of infrastructure components, such as the Identity Provider for managing digital identities, as well as monitoring components ensuring governance (i.e. that all participants are playing by the rules). EIDS is currently applying these components in a testbed, so that various application partners can experiment with them.
The image below shows the names of the companies and academic institutions taking part in the implementation and testing of EIDS. As far as the participating companies are concerned, two groups can be distinguished: companies providing infrastructure components and/or domain-specific additional components, and companies providing data and/or big-data enabling services in the form of applications and platforms.
The European Industrial Data Space (EIDS) can be considered a milestone on the way to the smart factory. EIDS is one of the first data spaces facilitating trade and commercial use of data without data owners losing sovereignty over their data. More data spaces based on the IDS standard are currently established, e.g. in the mobility sector.[3]
1] https://www.internationaldataspaces.org/wp-content/uploads/2019/03/IDS-Reference-Architecture-Model-3.0.pdf
[2] https://www.internationaldataspaces.org/ids-officially-a-standard-din-spec-27070-is-published/https://www.internationaldataspaces.org/ids-officially-a-standard-din-spec-27070-is-published/
[3] https://www.handelsblatt.com/politik/deutschland/autogipfel-merkel-draengt-autokonzerne-bmw-daimler-und-vw-sollen-datenschatz-teilen/26308418.html